Investigate entry points of attack and reduce cyber-attack risks
As corporate networks shift towards zero-trust thanks to increasing cloud use and teleworking, the entry points of malware (including ransomware) are also shifting. Moving from USBs and emails to network devices, cloud services, VPNs, and remote desktops is causing increasing damage.
Attack Surface Management (ASM) service reduces the risk of cyber-attacks by looking into IT assets (servers, network devices, clouds, etc.) that could be targeted by cyber attacks, reporting on their vulnerabilities, and identifying ID information exposed on the Internet.

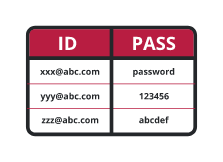
Attack Surface Management service uses the OpenSource INTELLIGENCE (OSINT) method to investigate open IT assets directly connected to the Internet, such as public servers and VPN gateways, as well as credentials (user IDs and passwords) leaked on the Internet. As cyber attackers use the same method to surveil target organisations, you can act as one of them to investigate the entry points of attacks and security risks of spoofing and take countermeasures for more urgent ones. Only the domain name is required for investigation, so it is possible to investigate your company's security risks and the entire supply chain, including overseas offices, group companies and business partners*.
*Supply chain surveys are carried out with the consent of the related companies.
(VPN/RDP/SSH/vulnerability etc.)
Service Menu |
Service Description |
|
One-shot survey service by experts
|
Survey reports for the current situation and measure proposal
|
|
Attack Surface Management cloud and investigation services
|
Hybrid version of one-shot service and ASM cloud
|